Listeners are tuning out. Sponsorship revenue has dipped. A diversity push has generated internal turmoil. Can America’s public radio network turn things around?

Listeners are tuning out. Sponsorship revenue has dipped. A diversity push has generated internal turmoil. Can America’s public radio network turn things around?


Stations everywhere take pride in having a main anchor who comes from the market they represent. That applies in St. Louis, too, but it also pertains to general managers. The bosses at KTVI-KPLR, KMOV and KSDK were all born and raised there. “St. Louisans love St. Louisans,” Kurt Krueger, KTVI-KPLR VP-GM says. “It gives me a special insight into what viewers like, and what they want to tune into.”

The industry trade group Adds Cintia Gabilan, VP of Media Center; Arlene Mu, assistant general counsel, and Nadine Karp McHugh, executive in residence.

Tubi, Fox’s free, ad-supported streamer, has partnered with British streaming service DAZN to add new channels featuring live and recorded women’s football, or soccer, as its known in the U.S., as well as boxing and MMA.

The new campaign represents "a significant milestone" in the BBC’s continued efforts to grow the recently relaunched BBC.com and BBC app throughout the world.
On Tuesday, Poynter unveiled the winners of its inaugural journalism contest, continuing a tradition that was most recently headed by the News Leaders Association. The Poynter Journalism Prizes saw over 525 entries from more than 300 news organizations and individual journalists. The contest was open to work across all platforms, including digital and broadcast, and featured 10 categories focused on different aspects of writing, reporting and leadership. Winners will receive a cash prize of $1,000 or $2,500, depending on the category. The broadcast winner is KHOU Houston.
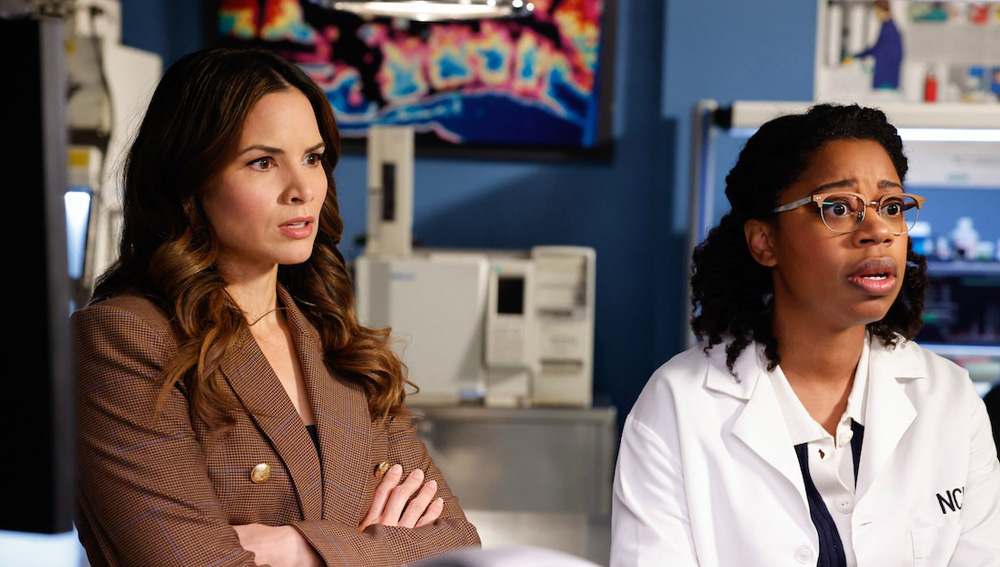
CBS's NCIS was Monday’s most-watched show 6.3 million/0.3), while NBC’s The Voice tied ABC’s American Idol for the nightly demo win (0.4).

Digital media data and analytics company DoubleVerify has received accreditation from the Media Rating Council for Video Viewable Impressions for connected TV (CTV). The company says this will help identify issues with advertisements that have run or played when TV sets are off.

President Joe Biden signed a foreign aid package that includes a bill that would ban TikTok if China-based parent company ByteDance fails to divest the app within a year. The divest-or-ban bill is now law, starting the clock for ByteDance to make its move. The company has an initial nine months to sort out a deal, though the president could extend that another three months if he sees progress.

The nation’s biggest business lobbying group and a national tax-services firm have sued the Federal Trade Commission.

If the Federal Trade Commission’s decision to ban noncompete agreements stands, anchors and many reporters should brace for the probability of seeing their salaries fall.

Kayla Thomas, creative services director of WLBT in Jackson, Miss., came up with a solution to balance commercial production and station promotion for two stations. “We are finally rolling like a well-oiled machine,” she says.

E.W. Scripps, one of the largest local TV broadcasters in the U.S., has hired a financial adviser to evaluate interest in acquiring Bounce TV, its over-the-air network geared toward African Americans, according to Scripps CEO Adam Symson.

Jo Ann Ross, the long-running queen of television advertising sales, is stepping down from her role as chairman of Paramount Advertising at the end of the month, the company says. A year ago, Ross was named chairman, taking an advisory role to Paramount Advertising President John Halley. The new move comes weeks before the upfront. Pictured: Jo Ann Ross with Jon Batiste's band during a CBS upfront at Carnegie Hall (CBS).
The streaming services will be looking for a larger share of the $27-billion pot for commercial time in the 2024-25 TV season.

The TikTok legislation was included as part of a larger $95 billion package that provides foreign aid to Ukraine and Israel and was passed 79-18. It now goes to President Joe Biden, who said in a statement immediately after passage that he will sign it Wednesday. Pictured: A TikTok content creator, speaks to reporters outside the U.S. Capitol on Tuesday, April 23, as Senators prepared to consider legislation that would force TikTok's China-based parent company to sell the social media platform under the threat of a ban, a contentious move by U.S. lawmakers. (Mariam Zuhaib/AP)

Some of the country’s most prominent legal commentators are holding off-the-record sessions to hash out the latest twists and turns in Donald Trump’s legal saga.

With the augmented reality advertising market expected to reach $14.5 billion in 2027 (up from $3.4 billion in 2022), the Interactive Advertising Bureau and the Media Rating Council have added game creator Niantic’s Rewarded AR ads technology to the set of ad industry measurement guidelines that both companies first released in February. “The Augmented Reality advertising market is projected to generate $1.2 billion in revenue in the U.S. this year,” explained Zoe Soon, vice president of IAB’s Experience Center, in February, adding: “Thus, as an industry, we need to establish a greater consistency on how we define and measure AR advertising to foster fairness and transparency for buyers and sellers.”

Katherine Maher says the controversy stemming from an editor’s essay criticizing the radio network has been a distraction.

Texas Attorney General Ken Paxton on Tuesday appealed an order that effectively blocked his investigation of the watchdog Media Matters, which issued a critical report about brand safety on the social platform X. Earlier this month, U.S. District Court Judge Amit Mehta in Washington prohibited Paxton from attempting to enforce a subpoena for a trove of information, ruling that he likely violated Media Matter's First Amendment rights by issuing the subpoena in retaliation for the group's report about ads on X. Paxton will ask the D.C. Circuit Court of Appeals to lift that injunction. The Texas official hasn't yet made substantive arguments to that court.

Jobs posted to TVNewsCheck’s Media Job Center include an opening for a director of sales and an account executive, executive producer, meteorologist, weekend anchor, sales manager, senior newscast producer, digital video producer and reporter.

Streaming sales leaders from Gray Television, E.W. Scripps, Hearst Television, Ticker and Megaphone TV will share the latest developments in technology and strategy for OTT and FAST channels. Learn more about this critically important revenue source for broadcasters in a TVNewsCheck Working Lunch Webinar on May 16. Register here.