Wall Street climbed Monday to kick off a big week for earnings reports. The rally was widespread, and most stocks across Wall Street rose.


Wall Street climbed Monday to kick off a big week for earnings reports. The rally was widespread, and most stocks across Wall Street rose.

The agreement would give the tech company worldwide rights for a monthlong World Cup-style competition between top teams set to take place next year.

The executive will join PENN Entertainment, which operates ESPN’s online sportsbook.

Technology company PubMatic is partnering with GroupM, the media investment group of WPP, to deliver cohort-based modeling capabilities for advertisers across multiple publishers, the companies say. The program uses a distributed AI model from Resolve, a Choreograph company.
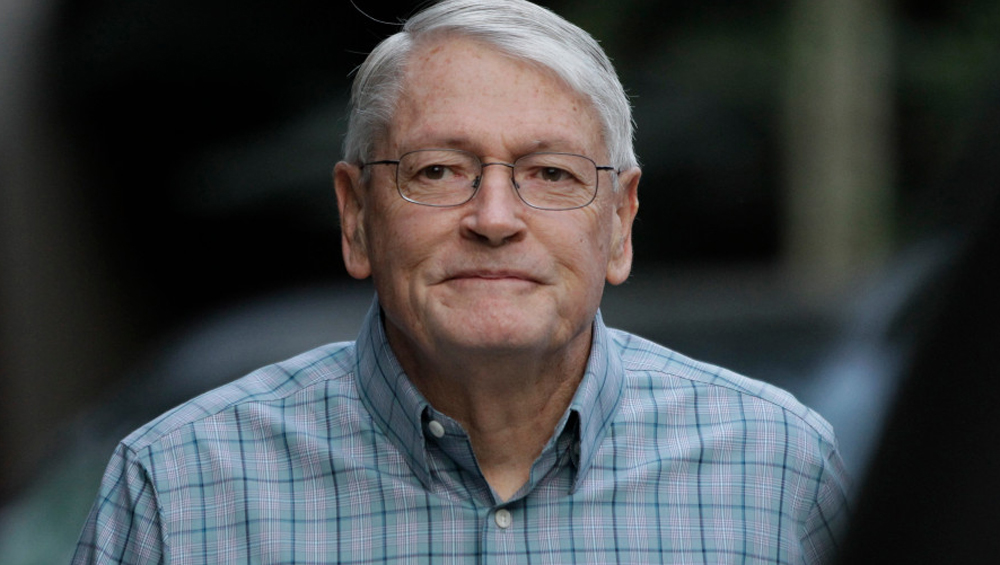
John Malone has stepped down from his role as director emeritus on the Charter Communications board, citing concerns that his simultaneous presence on Warner Bros. Discovery's board of directors violates the Clayton Act.

More than 100 newsrooms will receive $100,000 in general operating support over two years. Applications will be accepted April 30-June 12 at pressforward.news

The Indianapolis NBC-MeTV affils will air select Fever games following the Fever’s historic 2024 draft of Caitlin Clark.
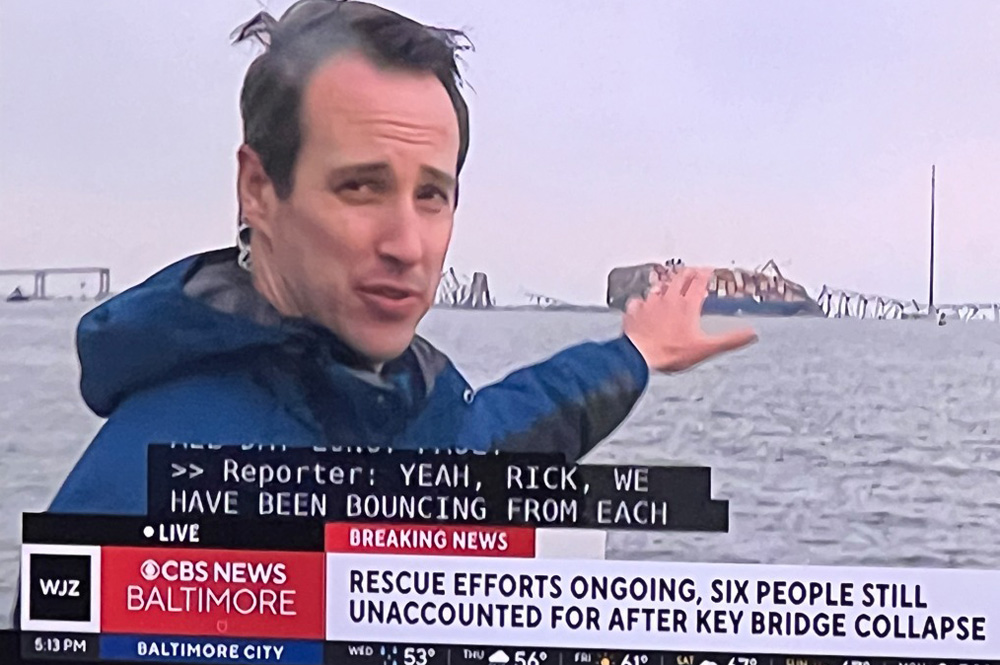
I have no doubt that all the Baltimore TV news teams responded quickly and fully and have their own stories to tell. This is part of what Baltimore’s CBS O&O, WJZ, did in the first hours as the magnitude of the tragedy unfolded.

Jobs posted to TVNewsCheck’s Media Job Center include an opening for a director of sales and an account executive, executive producer, meteorologist, weekend anchor, sales manager, senior newscast producer, digital video producer and reporter.

Six and a half months after Mark Thompson’s arrival at CNN (almost half of Chris Licht’s disastrous tenure), a restless and dour mood is once again enveloping the network. What is Thompson’s true plan, many wonder, and why won’t he articulate it?

Skydance Media CEO David Ellison, son of billionaire Larry Ellison, has emerged as a strong contender to take over the iconic Paramount studios.

There was both praise and criticism of the legal analyst and anchor, Laura Coates, and the network’s split-second decision to show the graphic footage.

The plan aims to support independent news organizations with three years of funding.

Many more people are jumping from one streaming subscription to another, a behavior that could have big implications for the entertainment industry.

Waves of layoffs and policy shifts are forcing campaigns to change tactics, potentially transforming the 2024 election.

Terry Anderson, the globe-trotting Associated Press correspondent who became one of America’s longest-held hostages after he was snatched from a street in war-torn Lebanon in 1985 and held for nearly seven years, died April 21 at 76. (Mark Duncan/AP)

After juicing its subscriber base to 270 million with a password-sharing crackdown, execs want Wall Street to stop focusing on subs and to look at other metrics, like its revenue, operating income and engagement.

The opening of the studios in Shreveport will aide in "fostering talent, creating opportunities, and building a community that thrives through creativity and innovation."

The new honor will recognize “Exemplary spirit and dedication” to the foundation’s mission. The inaugural award will be presented at next year’s Golden Mic dinner.

The fate of TikTok in the United States is even more uncertain as the House on Saturday voted on a package that requires that parent ByteDance divest its popular social media platform or face a ban on app stores. Lawmakers passed the bill 360-58, part of a series of votes to break a six-month standoff over a $95 billion aid package to Ukraine as well as to Israel and to Taiwan and the Indo-Pacific. The Senate is expected to take up the package of bills, including Ukraine, Israel and Taiwan aid, soon, perhaps as soon as April 23.

A preliminary injunction hearing for Fubo’s legal battle against Fox, Disney and Warner Bros. Discovery’s sports streaming joint venture has been set for Aug. 7 at 9:30 a.m. by the U.S. District Court for the Southern District of New York. The hearing will continue on Aug. 8 and Aug. 9, if necessary.

Writers Guild members at Sesame Workshop have reached a tentative deal with management to avoid a threatened strike. A ratification vote on the new five-year collective bargaining agreement will be held in the coming days. The writers had voted earlier to authorize a strike against the nonprofit organization, and picketing would have begun April 24 outside Sesame Workshop’s offices in New York City, had a deal not been struck.

Federal regulators on Friday announced a new plan designed to advance the interests of independent video programmers that have complained for years about restrictive contract terms demanded by pay TV distributors. FCC Chairwoman Jessica Rosenworcel said she launched the rulemaking in response to independent programmers that “continue to express concern about the challenges they have getting their programming on the channel lineup of cable and satellite television.”

CBS has canceled CSI: Vegas after three seasons and So Help Me Todd after two. That despite CSI: Vegas and So Help Me Todd being solid ratings performers. With the entire CBS schedule doing well this season and three new drama series joining in 2024-25 — NCIS: Origins, Matlock and Watson (in addition to a second season of the Australian NCIS: Sydney) — the network was faced with painful decisions, and So Help Me Todd and CSI: Vegas are the least watched CBS drama series this spring in both linear and multi-platform ratings.

Nexstar Media Group said it does not intend to renew the affiliations of The CW stations owned by E.W. Scripps in seven markets. In two of those markets — Norfolk, Va., and Lafayette, La. — Nexstar-owned stations will become the new The CW affiliates, effective Sept. 1. “We have interest from other station groups in the five remaining markets and expect to make announcements about those affiliations soon,” Nexstar said in a statement.

Streaming sales leaders from Gray Television, E.W. Scripps, Hearst Television, Ticker and Megaphone TV will share the latest developments in technology and strategy for OTT and FAST channels. Learn more about this critically important revenue source for broadcasters in a TVNewsCheck Working Lunch Webinar on May 16. Register here.