Cobalt Iron, a provider of SaaS-based enterprise data protection, has received a European patent on its technology for cyber event responsiveness, officially known as dynamic IT infrastructure optimization responsive to […]
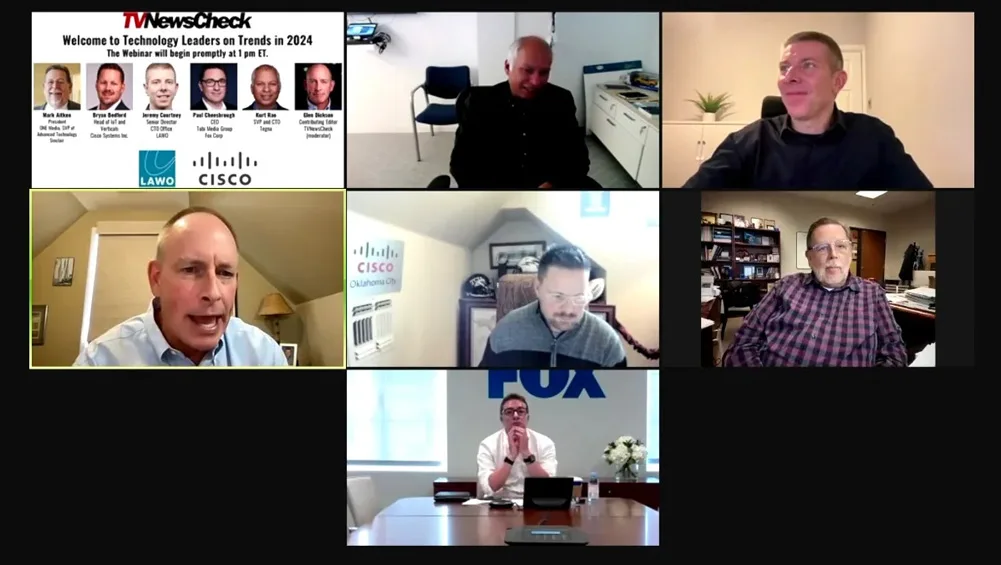
Top executives from Tubi, Tegna, Sinclair, Cisco and Lawo told a TVNewsCheck webinar Tuesday that hybrid technology architectures and business models would be a major dynamic in 2024, along with an expanding and promising use of generative AI that also compels great caution. To watch the video of the full webinar, click here.
Cobalt Iron Inc., a provider of SaaS-based enterprise data protection, today announced Isolated Vault Services, a new enhancement available in the Cobalt Iron Compass enterprise SaaS backup platform. “In a […]

In this repeat of the Talking TV episode from June 23, Brian Morris, CISO for Gray Television, says that building successful defenses against ever more frequent and sophisticated cyberattacks on broadcasters depends on having a strong culture of cybersecurity from the C-suite down. A full transcript of the conversation is included. For more information about TVNewsCheck‘s Cybersecurity for Broadcasters Retreat on Oct. 26, click here.

C-suiters from Gray Television, The Weather Group and Avid will share recommendations for how security leaders can effectively communicate the need for more cybersecurity investment to the CEO and board of directors in a special breakfast workshop at TVNewsCheck’s Cybersecurity for Broadcasters Retreat on Oct. 26 at the NAB Show New York. Register here.

In this repeat of the Talking TV episode from June 23, Brian Morris, CISO for Gray Television, says that building successful defenses against ever more frequent and sophisticated cyberattacks on broadcasters depends on having a strong culture of cybersecurity from the C-suite down. A full transcript of the conversation is included. For more information about TVNewsCheck‘s Cybersecurity for Broadcasters Retreat on Oct. 26, click here.

With the integration of IP and Information Technology (IT) into the core of broadcasting operations, the industry finds itself grappling with new vulnerabilities and threats – threats that are vastly different from those a decade ago. Then, the biggest fear was a rogue employee or stolen content. Today, ransomware hacking and larger denial-of-service (DoS) attacks are more than a threat – they’ve been experienced firsthand by major media organizations

Cobalt Iron, a provider of SaaS-based enterprise data protection, today announced that it has received a patent on its proactive technology for automated remediation of cyber and storage events. U.S. […]
Cyber Threats Demand That Broadcasters Work Together

The threats posed by cyberattacks are a common problem for everyone in the broadcasting industry. The only appropriate response is to work closely together across media companies and vendors alike.

Brian Morris, CISO of Gray Television, says that building successful defenses against ever more frequent and sophisticated cyberattacks on broadcasters depends on having a strong culture of cybersecurity from the C-suite down. A full transcript of the conversation is included. For more information about TVNewsCheck‘s Cybersecurity for Broadcasters Retreat on Oct. 26, click here.

CISA, the Federal Bureau of Investigation, the National Security Agency and the cybersecurity authorities of Australia, Canada, United Kingdom, Germany, Netherlands and New Zealand jointly developed Shifting the Balance of Cybersecurity Risk: Principles and Approaches for Security by Design-and-Default. This first-of-its-kind joint guidance urges manufacturers to take urgent steps necessary to ship products that are secure-by-design-and-default. In addition to specific technical recommendations, this guidance outlines several core principles to guide software manufacturers in building software security into their design processes prior to developing, configuring, and shipping their products.

A ranked-choice voting process allowed media companies and some participating vendors to agree on a list of the top 10 security priorities for the technology vendors serving the media industry. Key concerns included securing the media supply chain and complying with new insurance company rules requiring companies to regularly audit their security vendors.

Executives from Sinclair, Cox and Graham Media will explore the unique threats — and defenses — the media and entertainment industries manage around ransomware attacks in a panel at TVNewsCheck’s Cybersecurity for Broadcasters Retreat on Oct. 18. Register here.
Cybersecurity Returns To The Forefront: Five Rules Media Companies Need To Follow Now

While the war in Ukraine disrupted a number of cyber threat groups and the world was fooled into thinking cyberattacks were declining, cybercriminals have reorganized, are on the rise and show no sign of slowing again. Here’s some very tactical, practical advice and information media executives should consider as they’re forced to ramp up protections against cyber threats.

Cybersecurity executives from E.W. Scripps, Sinclair, Gray Television and Cox Media Group will confront the most serious security issues facing broadcasters in a time of escalating threat, offering guidance on averting crises on Oct. 19. Register for TV2025 here.

State-sponsored hackers from China, North Korea, Iran and Turkey have been regularly spying on and impersonating journalists from various media outlets in an effort to infiltrate their networks and gain access to sensitive information, according to a report released on Thursday by cybersecurity firm Proofpoint. The report reveals that government-backed hackers used various tools to target journalists, including sending phishing emails to gain access to reporters’ work emails, social media accounts and networks.

The World Broadcasting Unions has updated its list of Cybersecurity Recommendations for Media Vendors’ Systems, Software and Services, a document designed to help technology vendors enhance the security of their solutions. Media company IT and security managers also use the list, first released in 2018, as a framework for what to ask of their vendors when investing or maintaining their networks. Download a copy of the recommendations here.

Anne Neuberger, the deputy national security adviser for cyber and emerging technology, discusses how the battle in cyberspace is shaping up.

Broadcasters need an arsenal of ways to protect and mitigate against smarter ransomware attacks, particularly targeted against vulnerable CEOs as a “when,” not “if” predicament. These are the questions those CEOs should be asking.
SDP Needed For Broadcasters’ Cybersecurity Arsenal

The recent ransomware attack against Sinclair underscores broadcasters’ particularly acute vulnerabilities to data hacks. Software-designed perimeter (SDP) solutions are the weapons media companies need to fight back.

TV operations at several Sinclair-owned stations went down on Sunday in what the stations have described as technical issues, but which sources say is a ransomware attack. The incident occurred in the early hours of the day and took down the Sinclair internal corporate network, email servers, phone services and the broadcasting systems of TV stations.

When companies move all employee communications online, they face the same problems as the rest of the internet. But they don’t have to let bad behavior seep in.

Email remains one of the main ways through which attackers gain entry into broadcasters’ networks, and they change their methods of attack quickly. Good training not to click on suspect links is an essential defense. Above: Akamai multi-factor authentication access control on a smartwatch. Multi-factor authentication requires multiple pieces of identification before granting access.

In an environment where so many broadcasters have shifted to remote production and workflows, experts advise them to adopt layered defenses to protect their networks against a range of cybersecurity threats.
The media industry suffered 17 billion credential stuffing attacks between January 2018 and December 2019 according to a new report from Akamai, a global content delivery network, cybersecurity and cloud […]
Live virtual events for broadcasters this week focus on revenue as well as technology. They include an Akamai webinar on securing Javascripts, a Cisco presentation about Precision Timed Protocol in SMPTE 2110 Fabrics and the Sports Video Group’s annual College Sports Summit. TVNewsCheck will present Optimizing Spot TV in a Challenging Economy and BIA will focus on Selling Digital Marketing Services to Local Businesses. Media Financial Management Association continues its series of webinars for CFOs and other financial managers. For the full list of events and links to their registration pages, visit TVNewsCheck’s Virtual Events Directory.
Dalet, a global provider of solutions and services for broadcasters and content professionals, was awarded the DPP Security Marks for Production and Broadcast under “The DPP Committed to Security” program. The marks certify […]

A decade-long migration from hardware to software, underway in the media and entertainment industry, has been slowed by companies’ inability to coax engineering teams to collaborate with the growing ranks of IT managers being recruited into the industry. A roadmap, drawn up at a February Cybersecurity for Broadcasters Retreat in Orlando, offers a way forward.
View: AV-Over-IP Boosts Broadcast Security

The AV-over-IP stack is a growing function of broadcast technology that can’t be overlooked or ignored when it comes to management, observability, quality of signals and security.
CBR To Spotlight Security’s Role In M&A

Top cybersecurity executives from E.W. Scripps, Cox, Tegna and Sinclair will share their experiences with — and advice for — planning and executing secure mergers and acquisitions at TVNewsCheck’s third annual Cybersecurity for Broadcasters Retreat.

Brands lose about $235 million annually from unknowingly running ads alongside fake news, and in the upcoming 2020 presidential election $200 million will be spent on boosting, advertising and deploying fake news, according to a study that analyzes the direct economic cost from fake news.
Collins | Navigating Complex Privacy-Cybersecurity Laws

Companies that sustain a data breach must be aware of applicable federal, state and foreign laws. Breaches generate a mélange of regulatory investigations, lawsuits, fines, reputational damage, drops in stock prices and business disruption. Whose information is taken determines the company’s obligations. Preparation is the key to staying out of the news.
CBR 2020 To Focus On Engineering-IT-Security

Set for Feb. 12-13, 2020, in Orlando, Fla., TVNewsCheck’s annual Cybersecurity for Broadcasters Retreat will gather TV engineering, IT and security executives, managers and professionals to build collaborative strategies for enhancing security in the TV industry.
At IBC 2019 (Sept. 13-17, RAI Amsterdam), independent video software provider Synamedia will unveil enhancements to its security portfolio to help combat the evolving threat from hyper-distributed piracy in the age […]
Collins | Cybersecurity Is More Important Than Ever

Current cybercrime trends are revealing organizations’ cyber skills shortages. Given the escalation on the criminal side, companies need to speed their detection and intervention. Recommended approaches include automated detection processes using artificial intelligence and security orchestration, automation and response.

Lisa M. Fowlkes, chief of the FCC’s Public Safety and Homeland Security Bureau, says broadcasters play a vital role during emergencies and the public relies on them to stay informed, find resources and stay safe. “To continue fulfilling this important mission, broadcasters must ensure that their systems are secure and reliable. Here are some best practices to help.”
Don’t Learn About Cybersecurity The Hard Way

A recent ransomware attack gave Tribune Publishing a trial by fire in cybersecurity. The company’s lessons have broad implications for all media companies in an age of advanced risk.
R9B, a provider of advanced cybersecurity products, services and training said today it has been named a 2019 Infosec Award winner in three categories: R9B Hunt, which is executed via the […]